PicoCTF – Corrupted File
Corrupted File
Challenge_Author: Yahaya Meddy
Category: Forensics
Description
This file seems broken… or is it? Maybe a couple of bytes could make all the difference. Can you figure out how to bring it back to life? Download the file here.
Process
- Download the file from the Pico website or you can click “here” to download the file.
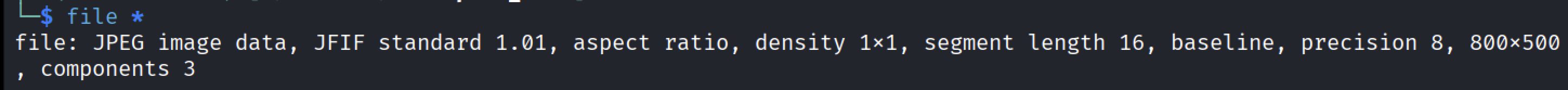
After downloading the file, I checked its type of data using the file command.
1 2
#Displaying the file format file *
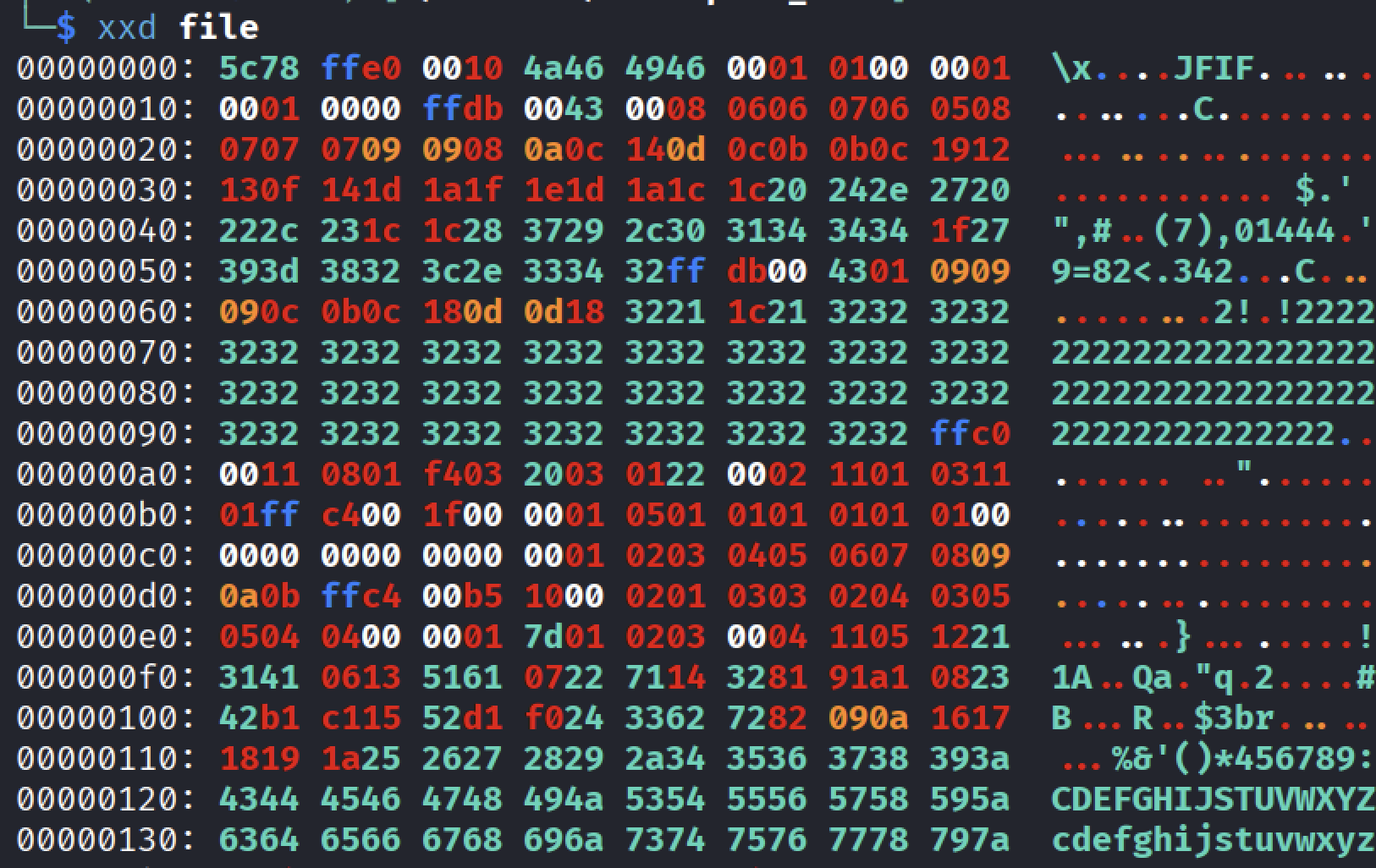
Since the output mentioned only “data” the only thing I can do is to look at the raw bytes using the “xxd” command.
1 2
#Displaying the hex values xxd file- Inspecting the starting bytes, I observed that it contains “JFIF” which is a part of the “JPEG” file format header.
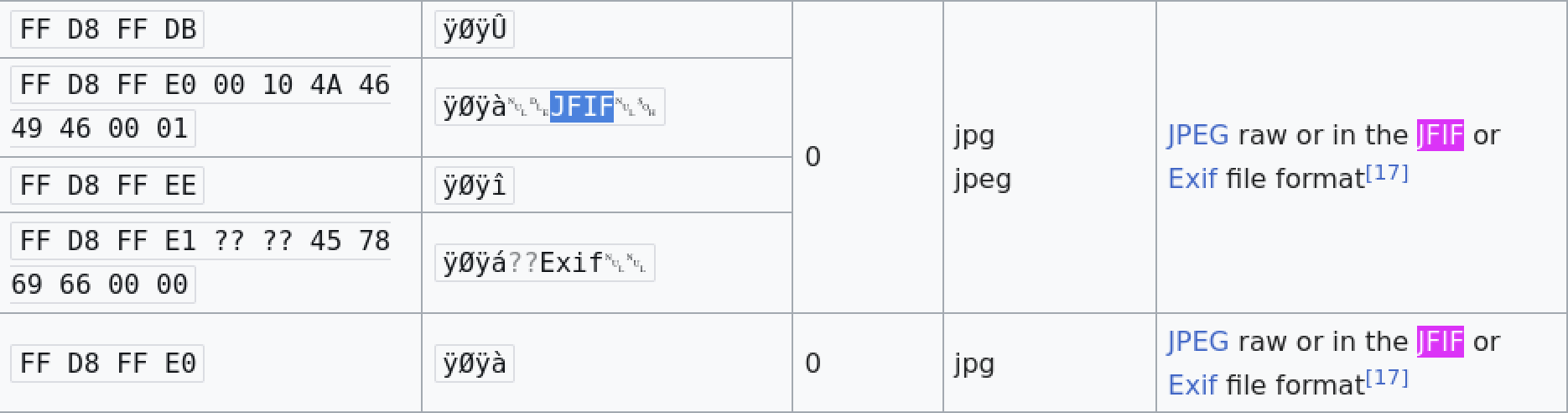
- Looking up on the internet, I found out that the first hex bytes were changed and which you can compare it in the wikipedia.
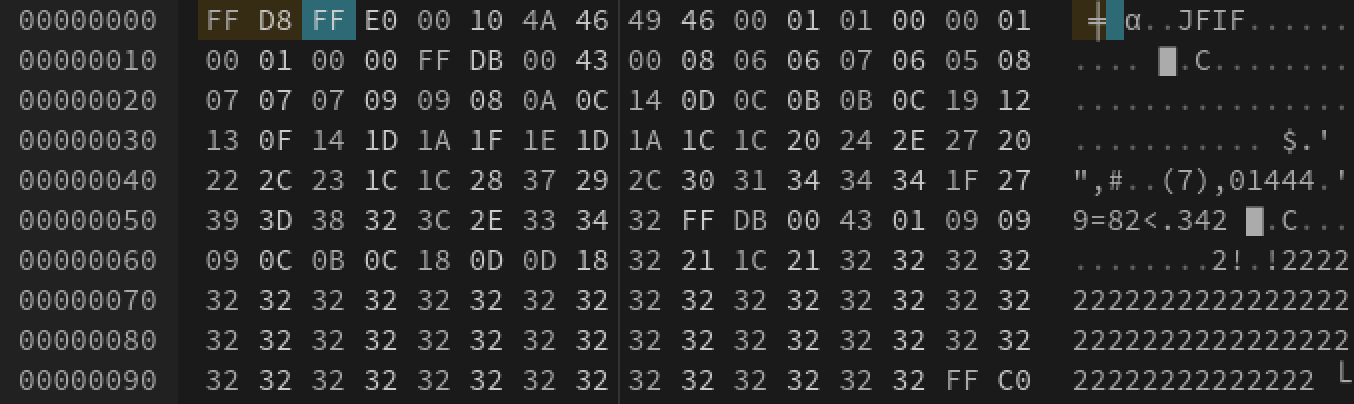
Using “Hexedit” or “Hexed.it” to edit the hex values.
- After changing the hex values, I exported the file.
Now inspecting the file type of the file once again to see any changes.
1 2
#Checking the file type file *
- Now the file type displays a “JPEG” file which is an image file.
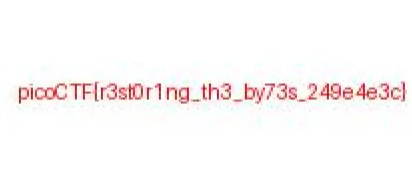
Using the “xdg” command to display the image.
1 2 3
```bash xdg-open file # -> thats the file name you can rename it to file.jpg ```
Finally the flag has been revealed.
1
picoCTF{r3st0r1ng_th3_by73s_249e4e3c}
Conclusion
This challenge highlights the importance of understanding file signatures and magic bytes in digital forensics. Even when a file appears broken or unrecognizable, a quick hex inspection can reveal clues about its true format. By restoring just a few critical bytes, the file was brought back to life and the hidden information was successfully recovered.
This is a great example of how low-level file analysis plays a crucial role in forensic investigations and CTF challenges alike.
Thanks for Reading
Thank you for taking the time to read this write-up! I hope it was helpful and informative. Happy hacking, and good luck with your future PicoCTF challenges 🚀