PicoCTF – Flag-In-Flame
Challenge_Author: Prince Niyonshuti N.
Category: Forensics
Description
The SOC team discovered a suspiciously large log file after a recent breach. When they opened it, they found an enormous block of encoded text instead of typical logs. Could there be something hidden within? Your mission is to inspect the resulting file and reveal the real purpose of it. The team is relying on your skills to uncover any concealed information within this unusual log.Download the encoded data here: Logs Data. Be prepared—the file is large, and examining it thoroughly is crucial.
Process
- The encoded log file was downloaded from the PicoCTF website
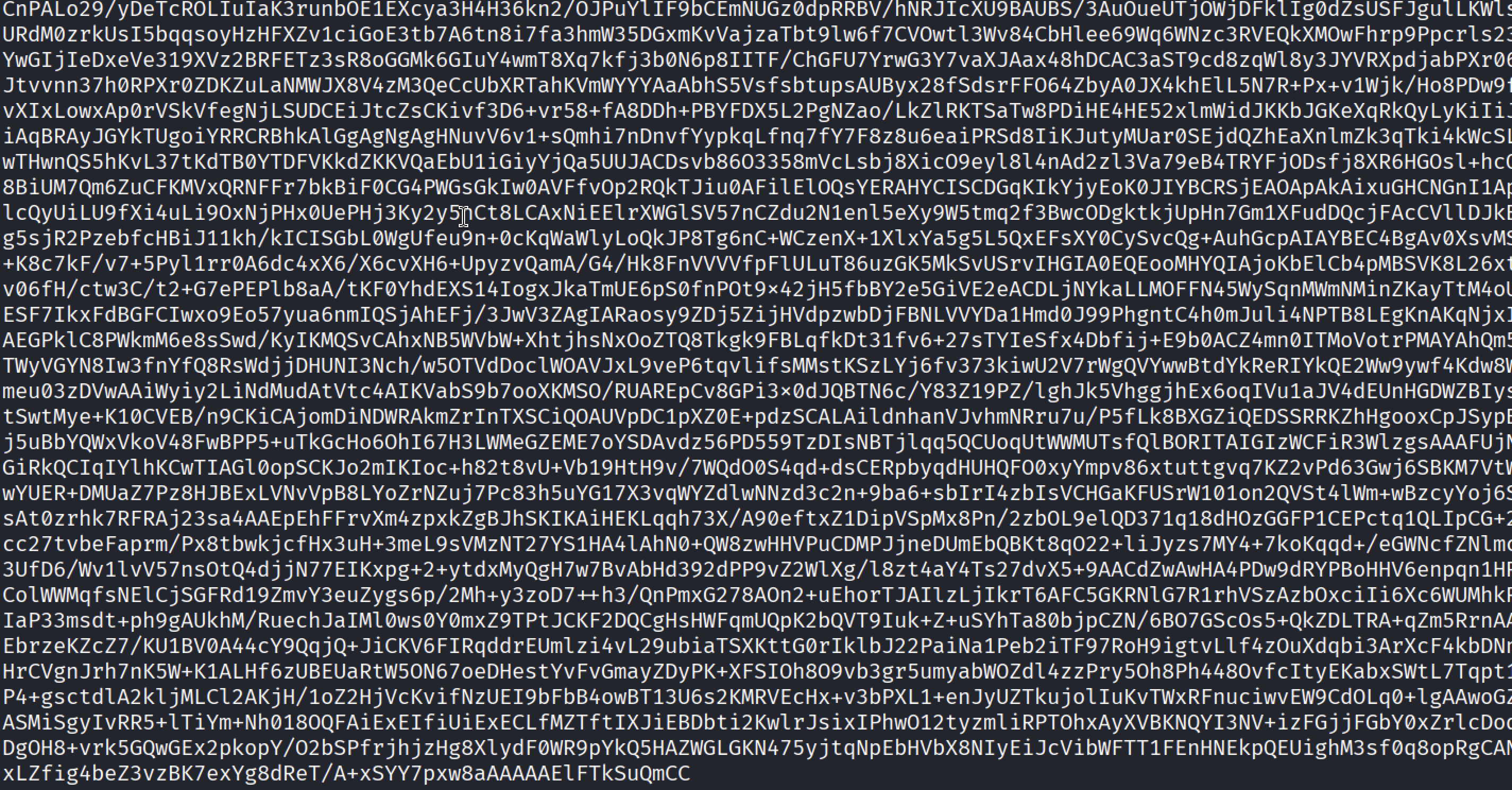
The contents of the file were initially inspected using the
catcommand, revealing a very large block of encoded data rather than readable logs.- Based on the structure and length of the data, it appeared to be Base64-encoded, as suggested in the challenge description.
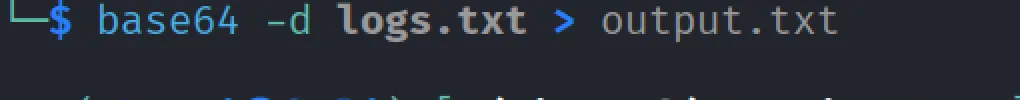
The entire file was decoded using the Base64 utility, and the output was redirected to a new file.
1 2
#Decoding the log file using base64 CLI tool base64 -d logs.txt > output.txt
After decoding, the
filecommand was used to identify the type of the resulting file.1 2
#Displaying the format of the file file *
The output indicated that the decoded data was a PNG image file. The file was then renamed accordingly.
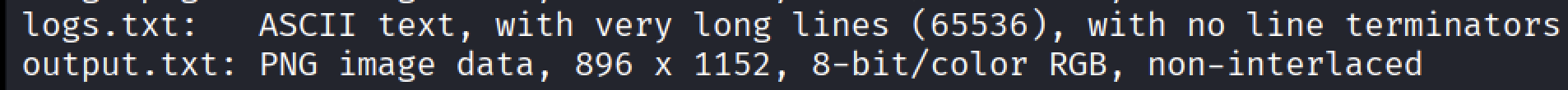
1 2
#Renaming the file mv output.txt image.png
The image was opened for inspection using the
xdg-opencommand.1 2
#Opening the image xdg-open image.png- Upon viewing the image, I observed that it contained another long encoded string embedded within the image itself.
The encoded text was extracted from the image using optical text recognition (OCR) assistance.
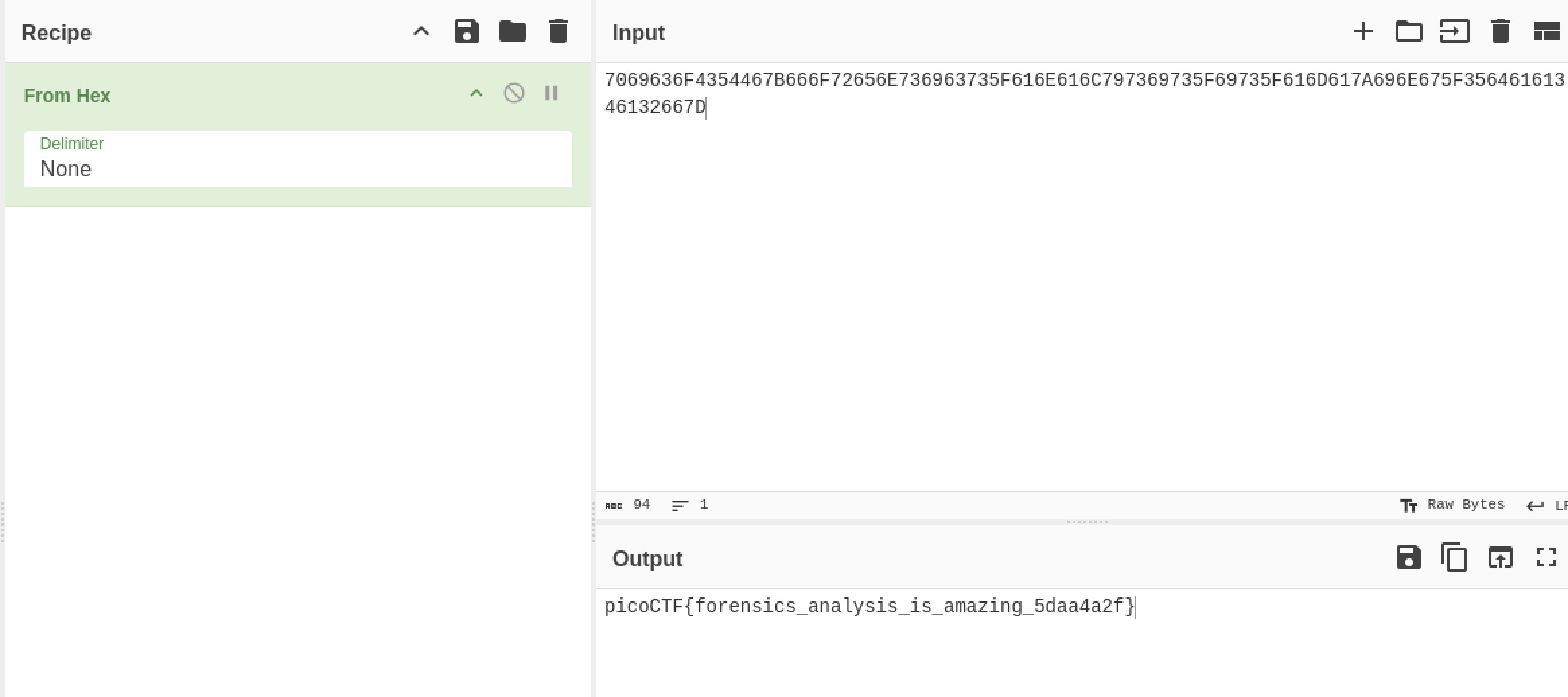
The extracted text was then analyzed and decoded using CyberChef, which revealed the final flag.
1 2
#Flag picoCTF{forensics_analysis_is_amazing_5daa4a2f}
Conclusion
This challenge demonstrated how seemingly ordinary files can conceal entirely different data types through encoding. By carefully inspecting the contents of the log file, identifying the Base64 encoding, and validating the decoded output using file analysis tools, the true nature of the data was revealed. The discovery of an embedded image containing another layer of encoded information reinforced the importance of thorough, step-by-step analysis in digital forensics.
This challenge emphasized key forensic principles such as verifying file formats, recognizing common encodings, and handling multi-layer data obfuscation—skills that are essential when investigating real-world security incidents.
Thank you for taking the time to read this write-up. I hope it clearly outlined the methodology and tools used to solve this forensics challenge. Stay curious, keep practicing, and happy hacking 🚀🔍