PicoCTF – Flag Hunters
Flag Hunters
Challenge_Author: syreal
Category: Reverse Engineering
Description
Lyrics jump from verses to the refrain kind of like a subroutine call. There’s a hidden refrain this program doesn’t print by default. Can you get it to print it? There might be something in it for you.The program’s source code can be downloaded here.
Process
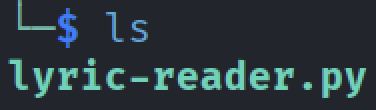
- Before Starting the Instance, I downloaded the provided Python file.
After downloading the file, I examined the contents. The file was a non-executable Python script, so I made it executable using the following command:
1
chmod +x lyric-reader.pyNow Executing the python file reveals the working of the program.
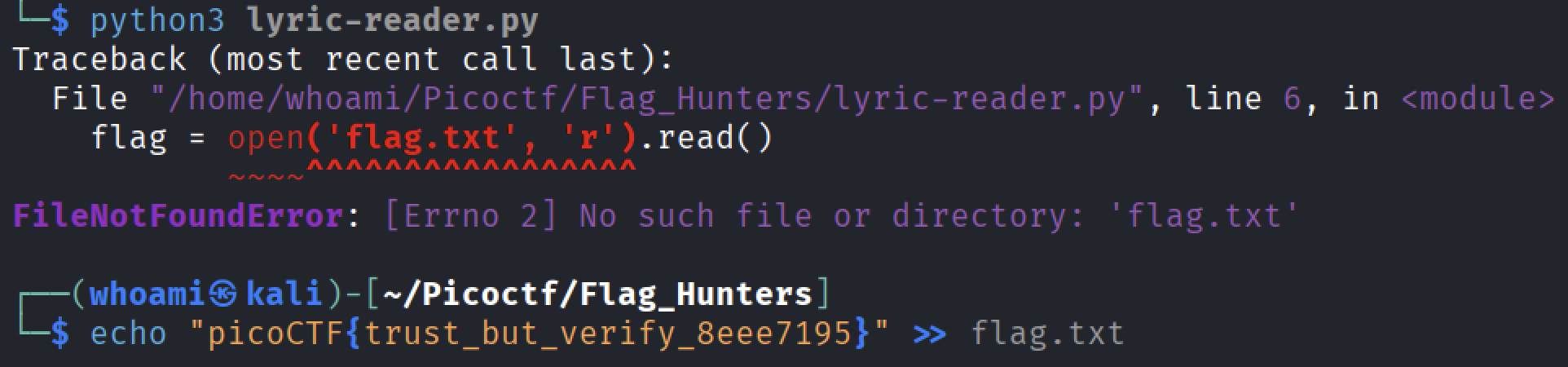
- Running the program initially revealed that it expected a
flag.txtfile. Since this file was missing, the program printed an error message. To continue testing locally, I created a placeholderflag.txtfile so that the program would execute normally. Now lets run the program in order to understand the working.
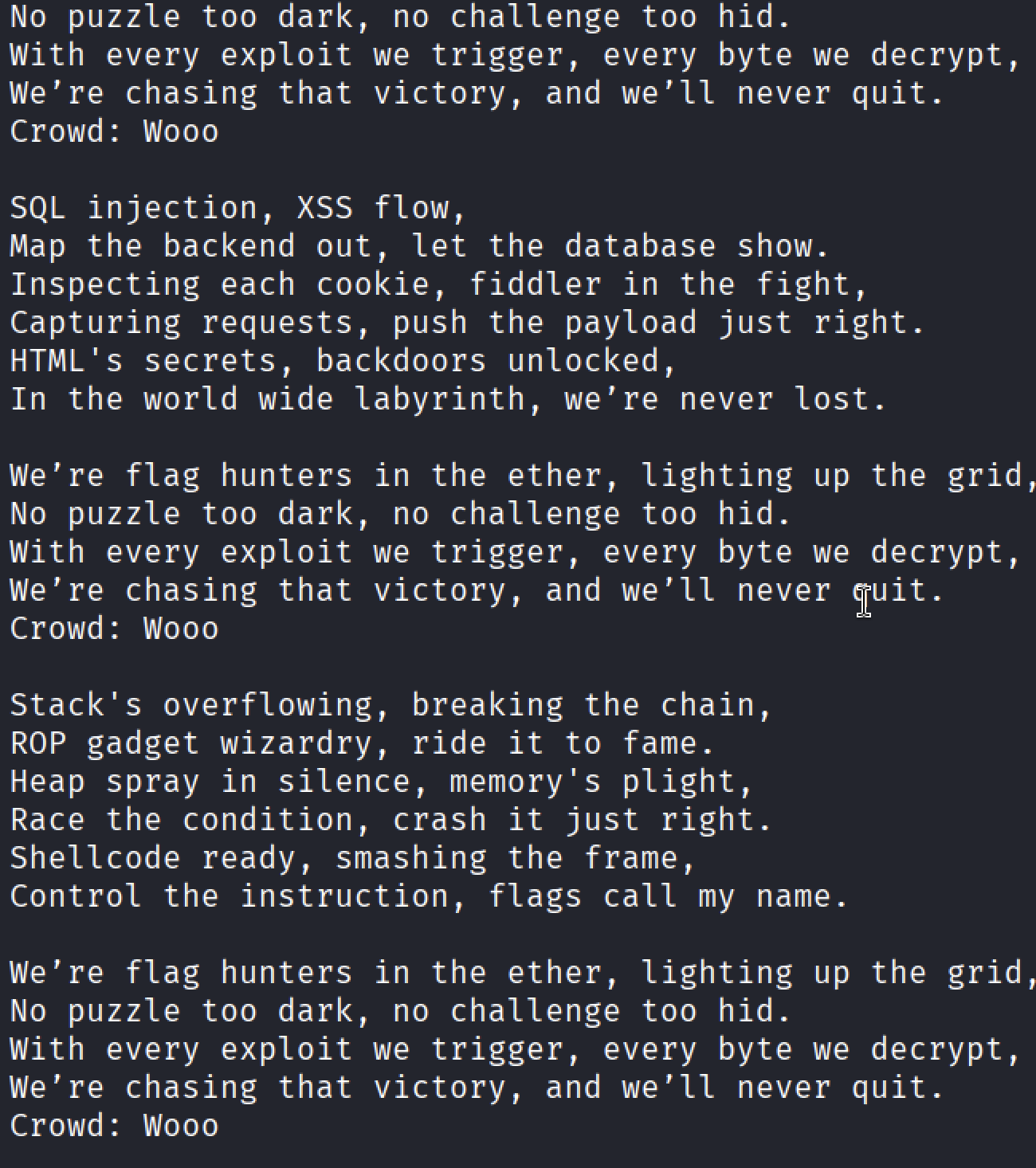
- Upon execution, the program prints a song line by line. At a certain point—during the “Crowd” section—it prompts the user for input. To observe how the program behaves, I initially entered a harmless string like: woo
The song continued and ended normally, with no hidden output displayed. This confirmed that user input directly affects execution flow, rather than being a simple text prompt.
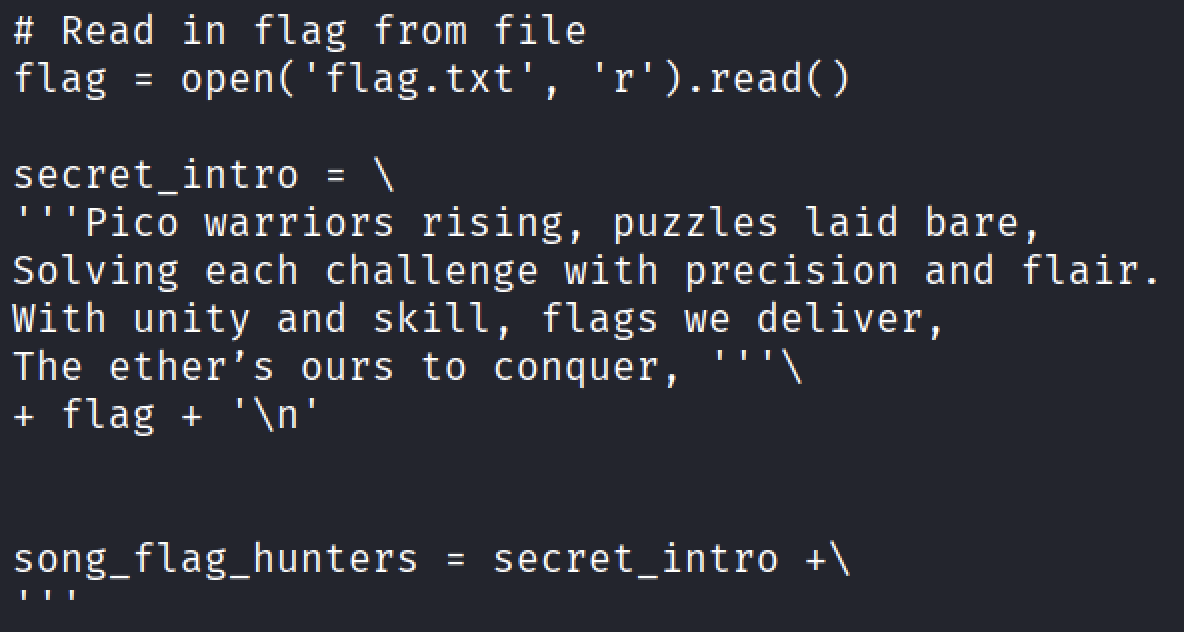
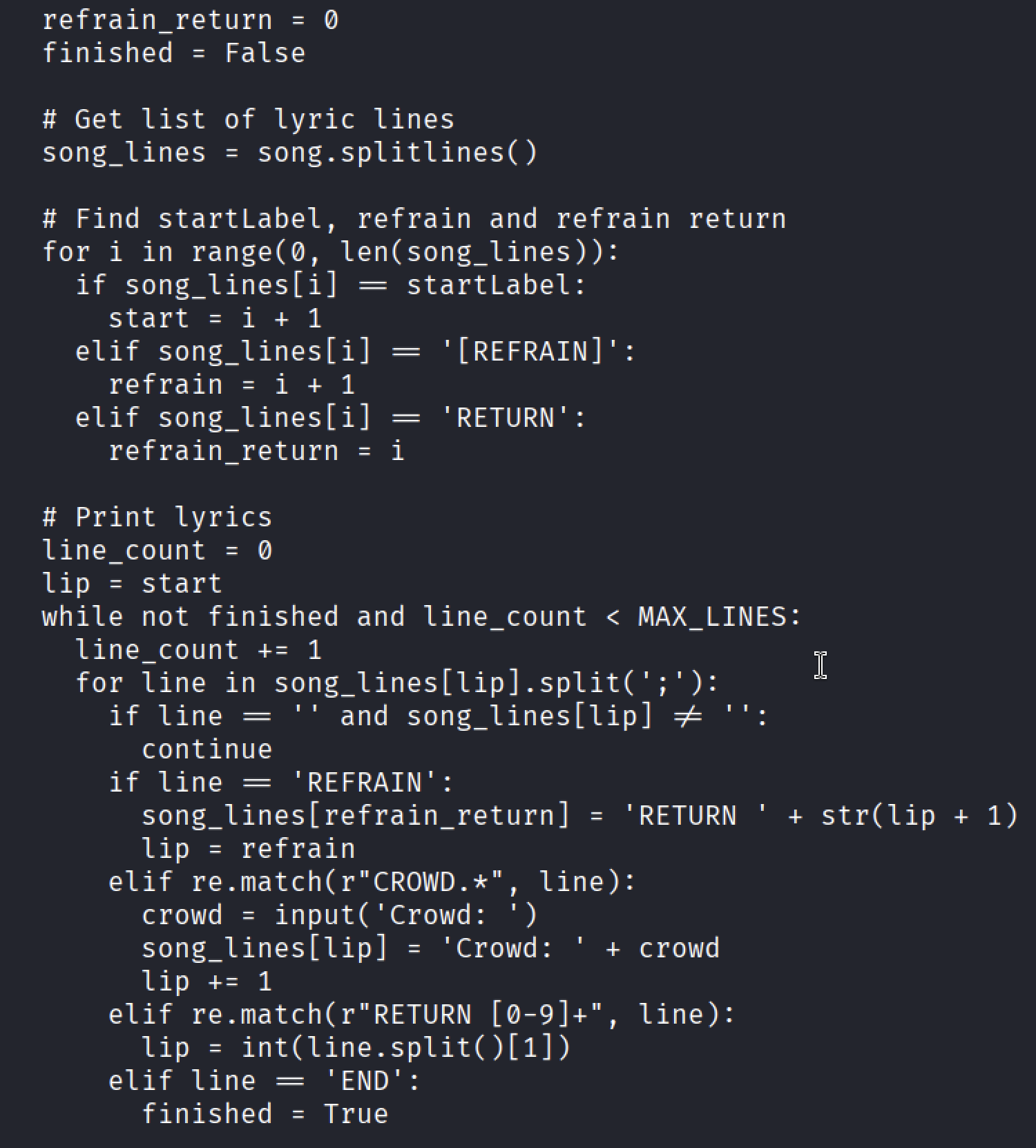
Examining the source code revealed several important behaviors:
At the beginning of the code, there is a hidden intro section that reads from
flag.txt. This section is not printed during normal execution.The program uses a custom instruction interpreter that:
- Splits lyric lines using
; - Iterates through them using an instruction pointer.
Supports control-flow commands such as
RETURN <number>The most critical discovery was this logic:1
elif re.match(r"RETURN [0-9]+", line):
If a
RETURNinstruction is encountered, the program jumps to a specific instruction index, similar to a function return or a jump instruction in assembly.This means:
If user input contains a valid RETURN instruction, it can redirect execution
- Splits lyric lines using
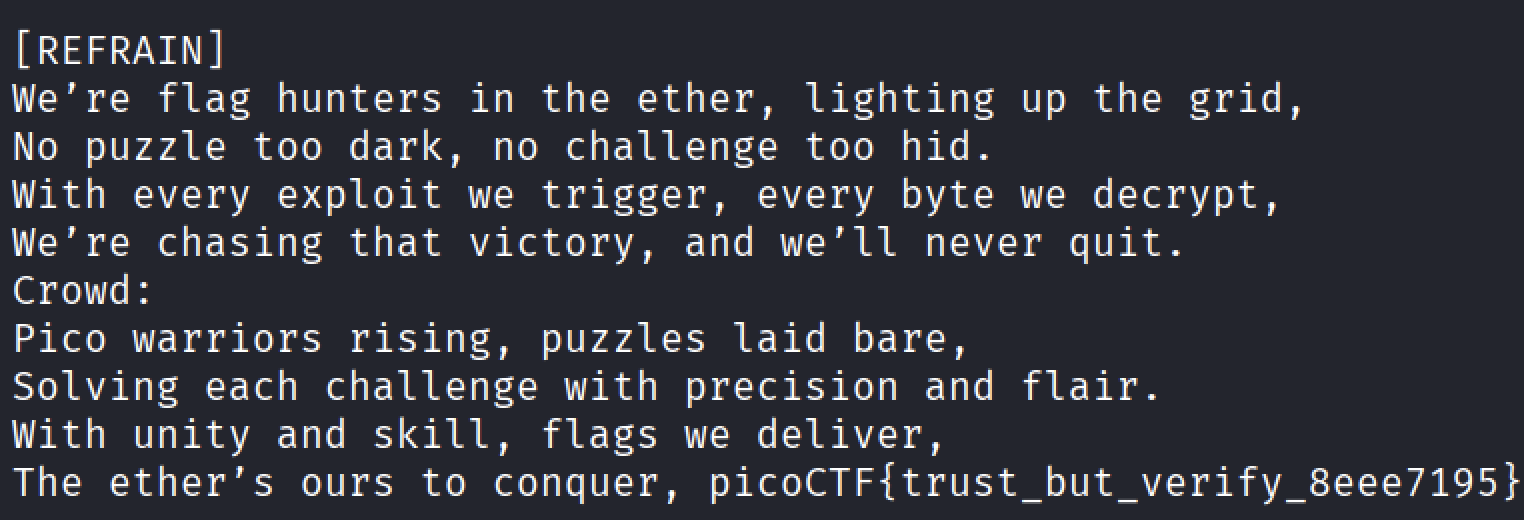
Re running the program, in order to test my solution.
- After Running the program, the program revealed the flag ( Not the original flag, just a place holder).
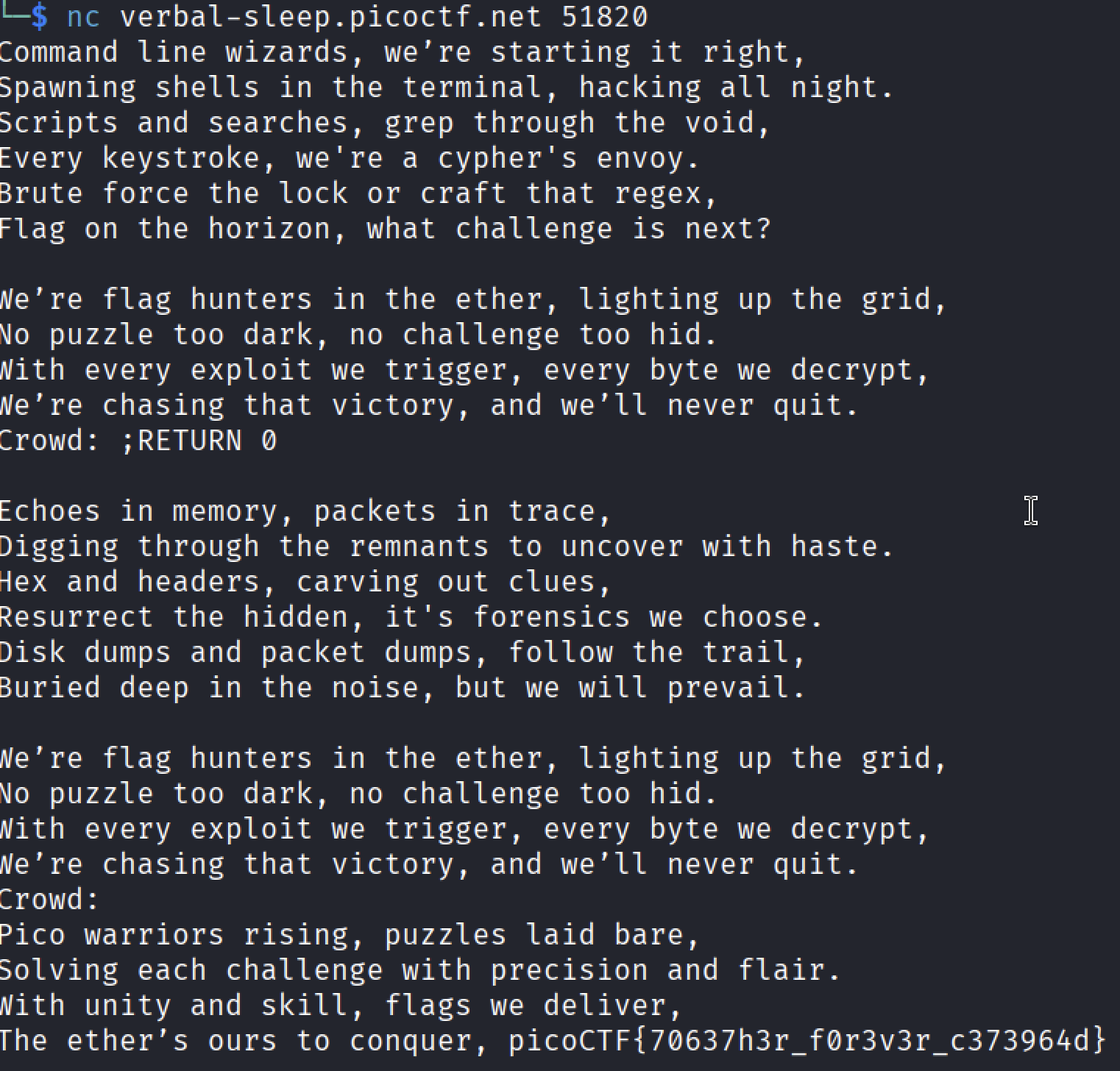
After starting the challenge instance on PicoCTF, I entered the following input when prompted.
This successfully redirected execution to the hidden intro, revealing the flag
1
picoCTF{70637h3r_f0r3v3r_c373964d}
Conclusion
This challenge demonstrates a classic reverse-engineering and exploitation concept:
- User input is treated as executable instructions
- Control over the instruction pointer enables unintended behavior
- A seemingly harmless input prompt becomes an execution vector
Key Takeaway
If user input controls program execution flow, the program is vulnerable.
This mirrors real-world exploitation techniques such as:
- Instruction pointer hijacking
- Return-oriented programming
- Interpreter abuse
Thank you to syreal and the PicoCTF team for creating such a clever and educational challenge. This problem beautifully bridges high-level Python logic with low-level reverse-engineering concepts, making it both fun and insightful see you in the next writeup.