PicoCTF – Crack The Gate 1
Crack the Gate 1
Challenge Author: Yahaya Meddy
Description
We’re in the middle of an investigation. One of our persons of interest, ctf player, is believed to be hiding sensitive data inside a restricted web portal. We’ve uncovered the email address he uses to log in: ctf-player@picoctf.org. Unfortunately, we don’t know the password, and the usual guessing techniques haven’t worked. But something feels off… it’s almost like the developer left a secret way in. Can you figure it out?
Additional details will be available after launching your challenge instance.
Process
- Launch the instance from the PicoCTF Website.
- After navigating to the website a login form will be displayed.
Using the email provided in the description with a common password failed to authenticate.
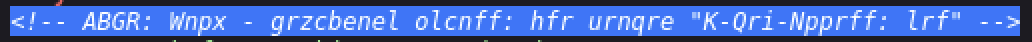
Looking at source code of the login form we can see that there is an “encoded message”.
Since the encoded message consisted only of shifted alphabetical characters, it was likely a Caesar cipher.
1
NOTE: Jack - temporary bypass: use header “X-Dev-Access: yes”
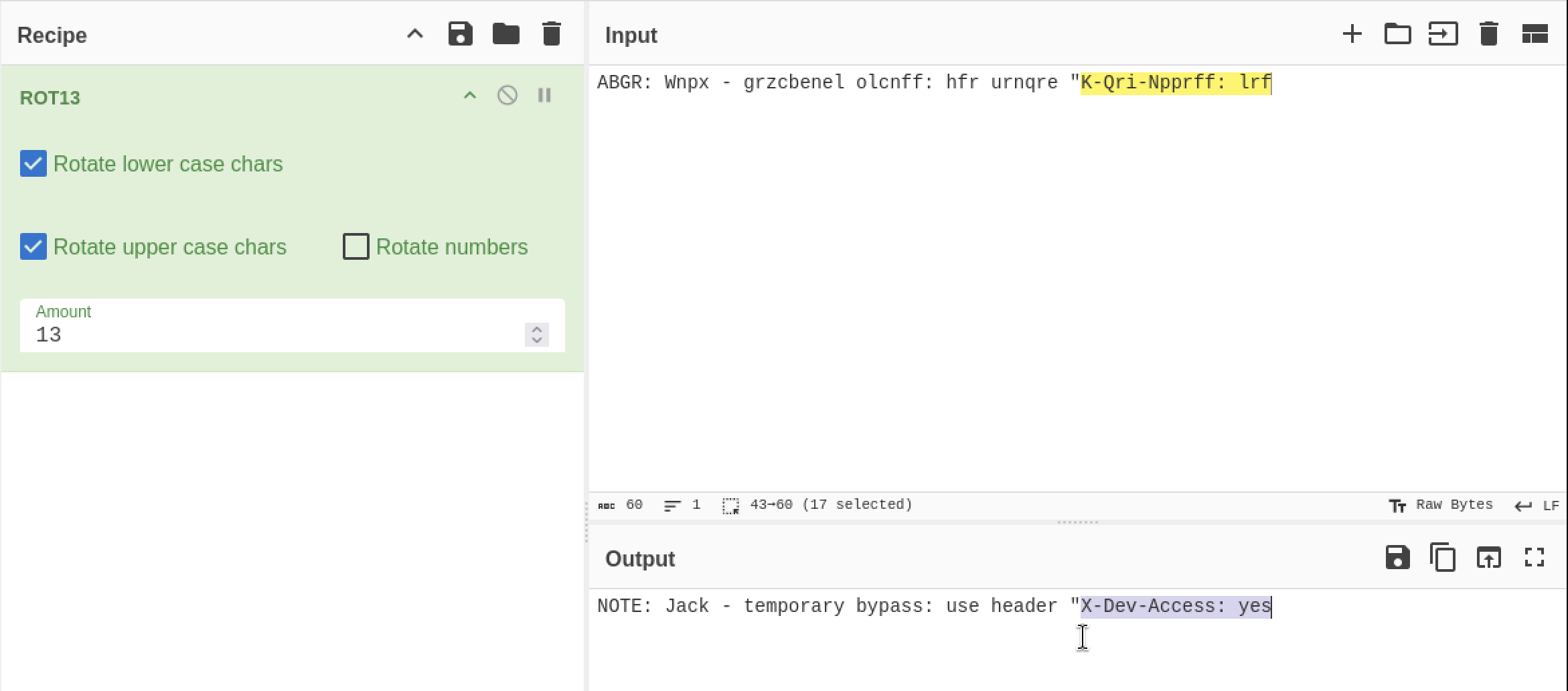
By this clue it means that we need add a “Request Header” which is the X-Dev-Access in the Request section which can be done in the Burpsuite.
- After Opening and Capturing the request and inserting the “X-Dev-Access” as yes and sending it I got the response as “200 OK” which gave the flag.
1
2
3
Flag: picoCTF{brut4_f0rc4_cbb8faa7}
Conclusion:
This challenge demonstrates the dangers of leaving developer backdoors in production code. By inspecting client-side source code and modifying HTTP headers, authentication was bypassed without brute forcing the password.